Zero Trust Security: A Practical Guide for Beginners
Zero Trust Security: A Practical Guide for Beginners
Zero Trust Security: Principles, Architecture, and Real-World Use Cases
A well-known principle of Zero Trust Security, on a lighter note, is that it is a security model where even the office printer has to prove its identity before sending a PDF. That's it. The message of this security model is clear - never trust, always verify. Technically, Zero Trust Security is a holistic IT security model that makes it absolutely necessary to strictly verify the identity of every person and device within or outside of the network perimeter.
Why does Zero Trust Security matter?
Zero Trust is a state-of-the-art cybersecurity framework that totally rules out even a remote possibility of letting any person and device unchecked, even though they are inside a company network. This sort of security measure is relentless in its approach of validating every request for accessing resources on a private network.
In Zero Trust Security, the verification process to identify anyone is technically a non-negotiable tactic, whether someone is working from the office, home, or a coffee shop. They must prove that they are authorized before they are allowed to access the systems of data. Based on the explanation, it is clear that Zero Trust Security holds utmost importance as one of the most viable security strategies adopted by businesses, governments, healthcare institutions, financial organisations, and cloud-first enterprises.

Industries adopting Zero Trust Security Framework
As a matter of fact, commercial ventures around the world are increasingly prioritizing the Zero Trust Security model, given the rise of sophisticated and coordinated cyberattacks too powerful for today's perimeter-based security systems.
Why Do Organisations Rely On Zero Trust Security?
Modern organisations around the world rely on Zero Trust Security because they use remote and hybrid work environments, cloud platforms and SaaS applications. Besides, their reliance on multi-cloud infrastructures, IoT devices, and BYOID (Bring Your Own Device) policies is also one of the factors driving them to rely on Zero Trust Security. Fact is, this security model not only ensures protection of the network but also resources from cyber dangers.
Key Principles of Zero Trust Security Model
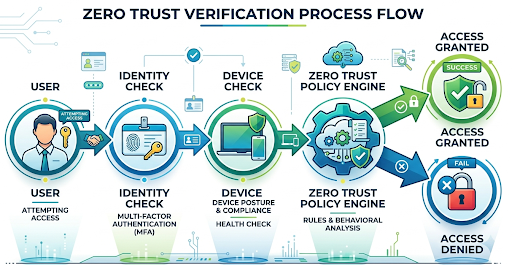
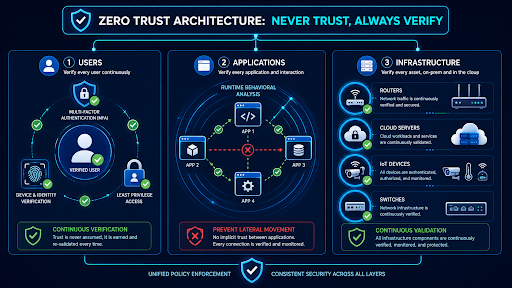
The security model of Zero Trust Security follows the maxim, "never trust, always verify" which essentially underscores its core principle of not to compromise network security and safety of resources. The principles like explicitly verify, use least-privileged access, and assume breach put the importance of this security model in center stage, where the use of it is a more logical strategy than trusting the outdated firewall-based security systems to protect sensitive data and digital assets.
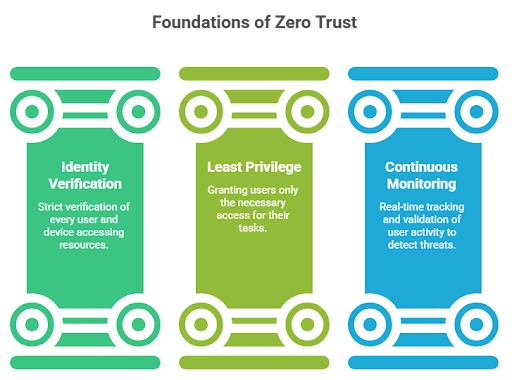
- Never trust, always verify - This is the clincher of Zero Trust Security model's core principle. It mandates pre-authorisation and pre-validation of any request for access to network resources. It involves evaluation of specific data points like identity, location, and device health. In simp;le words, this security measure does not allow automatic trust for any device or user or system.
- Least Privilege Access - Only minimum access with JIT (Just in Time) and JEA (Just enough Access) is granted to the users and devices.
- Micro-segmentation - Under this principle, Zero Trust Security, networks are divided into small, isolated and secure zones preventing attackers gaining access to data and high-value assets within the network.
- Continuous Monitoring - Real-time monitoring of unusual network activities.
- Assume Breach - Proactive detection and remediation of assumed network breach to improve the security posture and stay ahead of the sophisticated cyber threats.
Zero Trust Security model tends to evaluate every conceivable factor, from user identity, device posture, and geographic location to time of access, network behavior, risk score and application sensitivity.
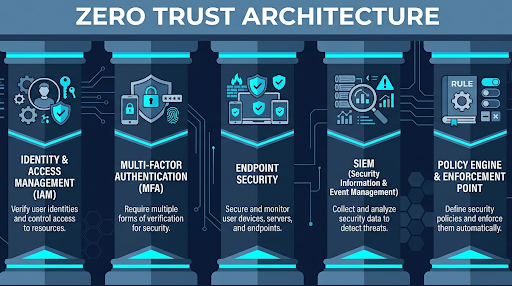
Zero Trust Architecture - A Modern Cybersecurity Framework
Zero Trust Architecture (ZTA) is a security framework that ensures that every access request to network resources is authenticated and authorized, based on its core principle: Never trust, always verify. The default working mechanism of ZTA is such that it untrusts every device, user, and application, whether they are inside or outside of the network. This approach of ZTA essentially serves as a key security strategy to reduce the attack surface, preventing hackers from gaining access to sensitive data, and protecting critical assets in a highly distributed digital environment.
Core Components of Zero Trust Architecture
Identity and Access Management (IAM)
In Zero Trust Architecture, identity is very important, considering security is no longer based on whether someone is inside or outside of the office network. In fact, it is based on who is trying to gain access to resources. It becomes also very important, in light of how cloud-native work and remote access are increasing the risk to the point that traditional networks are proving an unreliable safety net against cyber threats. IAM manages user identities, authentication methods, roles and access policies across a company's digital environment.
Common IAM Capabilities:
- Single sign-in (SSO) - One set of credentials to access multiple applications.
- Role based access control (RBAC) - Granting access based on job roles.
- Data synchronisation - Ensuring consistency in user data across all systems.
- Privileged access management - Monitoring privileged accounts and securing administrative credentials.
Mult-Factor Authentication (MFA)
Since passwords are no longer vital security parameters to protect sensitive systems, the role of MFA is crucial in the sense that two or more authentication steps, in all likelihood, are better protection layers than using just passwords.
MFA Factors:
- Something the user already knows like a password or a PIN.
- Sometimes users have a smartphone or a smart card.
- Something that represents users like fingerprint or facial recognition.
In a Zero Trust environment, the role of MFA is crucial in the sense that it prevents unauthorized access even if login credentials are compromised through phishing attacks, malware or credential leaks.
Endpoint Security
Endpoint security ensures safety of every connected device like laptops, smartphone, tablets, desktop, servers, and IoT devices by evaluating their health, compliance status and encryption settings, including suspicious behavior before granting them access. Sensing anything odd in the device like whether it is outdated, non-compliant or compromised, access is restricted or blocked permanently. Endpoint Detection and Response (EDR) tools are used to monitor threats, detect malware and respond to suspicious activities in real time.
Security Information and Event Management (SIEM)
SIEM platforms (e.g. IBM QRadar) act like a central security control room, ensuring centralised visibility into security events across infrastructure of an organization by collecting, monitoring and analysing security-related data. SIEM tools (e.g. IBM QRadar) play their role in the detection of suspicious behavior, unauthorized access attempts, and potential threats in real time. In simple words, SIEM actually gives power to an organisation's ability to enforce Zero Trust principles practically and effectively.
Policy Engine (PE) and Policy Enforcement Point (PEP)
Policy Engine (PE) and Policy Enforcement Point ensure automating security governance to maintain compliance, consistency and centralised control over network resources within a modern Zero Trust Architecture. They are the power players determining whether a user or a device deserve access to specific resources. The policy engine, for instance, evaluates factors such as user identity, device health, time of access, location, behavior patterns, and risk scores before decision to allow access is determined. The role of PEP steps in when the decision is made, ensuring whether the access is allowed, denied or restricted.
Zero Trust Security - Real World Use Cases
|
Use Case |
How Zero Trust Helps |
Key Security Benefits |
|
Remote Workforce Security |
Verifies employee identities, device health, and access requests for remote and hybrid workers. |
Prevents unauthorized access, secures remote devices, reduces VPN-related risks. |
|
Healthcare Industry |
Protects electronic health records, medical devices, and hospital systems using strict access controls and continuous monitoring. |
Reduces ransomware risks, safeguards patient data, supports healthcare compliance. |
|
Financial Services |
Secures banking systems, financial transactions, and customer accounts through strong authentication and behavioral analysis. |
Prevents fraud, limits insider threats, enhances regulatory compliance. |
|
Government and Defense |
Verifies every user, device, and application accessing sensitive government infrastructure and classified information. |
Protects national infrastructure, reduces espionage risks, improves cyber resilience. |
|
Cloud-Native Enterprises |
Secures cloud workloads, SaaS applications, and hybrid environments with identity-based access controls. |
Improves cloud visibility, reduces attack surfaces, secures distributed systems. |
|
Education Sector |
Protects student records, research databases, and online learning platforms through least privilege access and continuous verification. |
Prevents unauthorized access, reduces phishing risks, secures academic data. |
|
Manufacturing and Industrial Systems |
Secures operational technology (OT), industrial networks, and connected devices using segmentation and continuous monitoring. |
Prevents operational disruption, limits lateral movement, protects supply chains. |
|
Retail and E-Commerce |
Protects customer payment data, online transactions, and employee systems through identity verification and access controls. |
Reduces payment fraud, secures customer information, minimizes breach impact. |
|
IT and Technology Companies |
Secures developer environments, cloud infrastructure, APIs, and internal systems with adaptive authentication and segmentation. |
Protects intellectual property, reduces insider threats, secures software development environments. |
|
Telecommunications |
Protects telecom infrastructure, customer networks, and communication systems using strict authentication and network isolation. |
Prevents network compromise, protects subscriber data, improves service continuity. |
|
Energy and Utilities |
Secures power grids, water systems, and energy infrastructure against cyberattacks using continuous monitoring and restricted access. |
Protects critical infrastructure, reduces sabotage risks, enhances operational security. |
|
Third-Party Vendor Access |
Limits and monitors access provided to contractors, vendors, and external partners. |
Reduces supply chain risks, prevents excessive permissions, improves visibility. |
|
Data Centers |
Applies microsegmentation and access controls to critical servers and storage systems. |
Prevents lateral movement, strengthens data protection, improves monitoring. |
|
Internet of Things (IoT) Environments |
Continuously validates IoT devices and isolates compromised endpoints from the broader network. |
Reduces IoT vulnerabilities, limits unauthorized access, improves device security. |
|
DevOps and CI/CD Pipelines |
Secures software development pipelines through identity verification and policy-based access controls. |
Protects source code, reduces deployment risks, strengthens application security. |
Winding up
Zero Trust Security as a security model known for its stringent protection measures to proactively defend network resources has become mainstream priority for renowned companies like Microsoft, Paolo, Alto Networks, and Cloudflare. Constructed as one of the most effective cybersecurity frameworks in the modern business digital era, the security model is now an efficient replacement for traditional perimeter-based defenses, considering such defenses are proving inefficient for environments dominated by cloud computing, remote work and sophisticated cyber threats.
Zero Trust Security - FAQs
Is Zero Trust Security a product?
No, it is not a product. It is basically a cybersecurity framework rather than standalone technology. Companies use this security framework to better defend their network resources and improve operational efficiency.
Is the future of Zero Trust Security weak or strong?
The future of Zero Trust Security is strong, considering application of the security model is being adopted by organisations worldwide. In future, it is likely to become more automated, AI-assisted and adaptive in real-time.
Does Zero Trust Security replace VPNs?
Based on the trend, Zero Trust Security or zero trust network access (ZTNA) is fast replacing traditional VPN, ensuring users gain secure remote access. Zero trust evaluates each user, device and application request in real time, ensuring safety of the network resources, and also easier management for hybrid environments.
Is Zero Trust only for large organisations?
Apart from large organisations, Zero Trust finds its application in small and medium size businesses.
What are the key benefits of Zero Trust Security?
Zero Trust Security is fast becoming the most important replacement for traditional defense systems, as organisations are adapting cloud-native businesses and remote work cultures. Therefore, benefits of this security model include better security by enforcing least privilege access, protection against data breach through authentication of every request attempt, and reducing the impacts of sophisticated attacks by isolating network segments.